当前位置:网站首页>Explanation of penetration test process and methodology (Introduction to web security 04)
Explanation of penetration test process and methodology (Introduction to web security 04)
2022-06-23 05:49:00 【Black Warrior】
One 、 Penetration testing methodology
1.1 Penetration test (penetration testing,pentest)
It's a safety assessment ( Audit ) The specific means of .
Methodology is making 、 When implementing the information security audit program , Rules to follow 、 Routines and processes .
People are evaluating the Internet 、 application 、 System or a combination of the three , Constantly explore various practical ideas and maturity
How to do it , And summed up a set of theories —— Penetration testing methodology .
1.2 Type of penetration test
1.2.1 Black box testing
During the black box test , The safety auditor does not know the internal technical structure of the tested unit , From external evaluation network
Network infrastructure security .
At all stages of penetration testing , Black box testing uses real-world hacking techniques , Expose the security of the target , even to the extent that
It can expose security weaknesses that have not been exploited by others .
Penetration testers should be able to understand security vulnerabilities , Classify them and rank them according to their risk levels ( High-risk 、 Middle risk 、 Low risk 、 Information disclosure )
Sort it out . Generally speaking , The level of risk depends on the size of the harm that may be caused by the relevant weakness . Experienced penetration testing expert
It shall be possible to identify all attack modes that can cause security incidents .
When the tester has finished all the testing work of the black box test , They will send necessary letters related to the safety status of the test object
I'll sort it out , And use business language to describe these identified risks , And then they are summarized into a written report . black
The market price of box test is usually higher than that of white box test .
1.2.2 White box testing
The auditor of the white box test can obtain all kinds of internal data or even non-public data of the tested unit , So the penetration tester
Our vision is wider .
If the white box test method is used to evaluate the security vulnerability , Testers can achieve the highest evaluation accuracy with the least amount of work .
White box testing starts from the environment of the system under test , Eliminate all internal security issues . Thus increasing the penetration system from the outside of the unit
The difficulty of the system . Black box testing doesn't do that . White box testing takes as many steps as black box testing .
in addition , If you can combine white box testing with the regular R & D life cycle , Security can be found and even used by intruders
Before weakness , Eliminate all security risks as early as possible , This makes the white box test time 、 cost , And discovery 、 Explain
The technical threshold for solving security vulnerabilities is lower than that of black box testing .
1.2.3 Vulnerability assessment and penetration testing
Vulnerability assessment analyzes the situation and degree of security threats to enterprise assets , Evaluate the safety of internal and external safety controls
Totality .
This technical information system evaluation , Not only expose the risks in the existing preventive measures , And multiple alternatives should be proposed
Remedial strategies , And compare these strategies .
Internal vulnerability assessment can ensure the security of internal system , The external vulnerability assessment is to verify the boundary protection
(perimeter defenses) The effectiveness of the .
Whether internal vulnerability assessment or external vulnerability assessment , Evaluators will use various attack modes to strictly test
Security of network assets , So as to verify the ability of the information system to deal with security threats , Then determine the effectiveness of response measures .
Different types of vulnerability assessment require testing processes 、 Testing tools and automated testing techniques are also different . This can be done through a
Integrated security vulnerability management (vulnerability management) Platform .
The current security vulnerability management platform has a vulnerability database that can be updated automatically , Be able to test different types of network devices , and
And will not affect the integrity of configuration management and change management .
The biggest difference between vulnerability assessment and penetration testing is : Penetration testing should not only identify the weaknesses of the target , It is also designed in
Exploit on the target system 、 Privilege promotion and access maintenance .
let me put it another way , Although vulnerability assessment can fully find defects in the system , But we will not consider to measure the impact of these defects on the system
Harm done .
in addition , Compared with vulnerability assessment , Penetration tests tend to invade , Will deliberately use various technical means to exploit security vulnerabilities ;
Therefore, penetration testing may have a real destructive impact on the production environment . Vulnerability assessment is non intrusive , qualitative 、
Quantitatively identify known security vulnerabilities .
1.3 Safety testing methodology
1.3.1 open web Application Security Project (Open Web Aplication Security
Project ,OWASP)
1、’ Test Guide https://www.owasp.org/index.php/OWASP_Testing_Project
2、 Developer's Guide https://www.owasp.org/index.php/Gategory:OWASP_Top_Ten_Project
3、 Code review OWASP top 10(Web Top ten security vulnerabilities )
top ten Web Application security risks
1、 Inject . When untrusted data is sent to the interpreter as part of a command or query , There will be things like SQL,
NoSQL,OS and LDAP Injection vulnerabilities such as injection . An attacker's malicious data may induce the interpreter to execute an undeclared
Access to data by expected command or without proper authorization .
2、 Invalid Authentication . Application functions related to authentication and session management are often incorrectly implemented , from
So that the attacker can break the password , Key or session token , Or use other implementation defects to temporarily or permanently assume
Identity of other users .
3、 Sensitive data exposure . many Web Applications and API Unable to properly protect sensitive data , For example, finance , Medical insurance
healthy . Attackers may steal or modify these unprotected data , For credit card fraud , Identity theft
Or other crimes . Sensitive data can be compromised without additional protection , For example, static encryption or transmission
encryption , And special precautions need to be taken when exchanging with browsers .
4、XML External entities (XXE). A lot of older or improperly configured XML The processor evaluates XML In document
External entity references . External entities can use files URI The handler , Internal file sharing , Internal port scan , far
Program code execution and denial of service attacks to expose internal files .
5、 Invalid access control . Usually , Restrictions on the actions that an authenticated user is allowed to perform are usually not performed correctly .
Attackers can exploit these vulnerabilities to access unauthorized functions and services / Or data , For example, access to other users' accounts ,
View sensitive files , Modify other users' data , Change access rights, etc .
6、 Security configuration error . Security configuration errors are the most common problem . This is usually due to an insecure default configuration , No
Complete or temporary configuration , Open Cloud Storage , Misconfigured HTTP Headers and detailed errors containing sensitive information
Caused by messages . Not only must all operating systems be configured safely , frame , Libraries and Applications , But also must reach
Repair it when necessary / upgrade .
7、 Cross-site scripting XSS. Every time an application contains a new web page that is not protected by... Without proper authentication or escape
Trusted data , Or you can create HTML or JavaScript Browser API Update with user supplied data
Existing web pages , Will happen XSS Loophole .XSS Allows attackers to execute scripts in the victim's browser , These feet
This could hijack user sessions , Destroy a website or redirect users to malicious sites .
8、 Unsafe deserialization . Unsafe deserialization usually results in remote code execution . Even if the deserialization defect
Does not cause remote code execution , They can also be used to perform attacks , Including replay attacks , Inject attacks and privileges
Level attack .
9、 Using components with known vulnerabilities . Such as the library , Components such as frameworks and other software modules in the same way as applications
Privileged operation . If vulnerable components are used , Such an attack may result in serious data loss or server
To take over . Applications that use components with known vulnerabilities and API May damage application defense , And cause various attacks
Impact and influence .
10、 Insufficient logging and monitoring . Inadequate logging and monitoring , Plus missing or invalid integration of event responses , Make the attacker
Can further attack the system , Stay persistent , Turning to more systems and tampering with , Extract or destroy data . Most violate
Regular research shows that , Violations were detected for more than 200 God , It is usually done by external parties rather than internal processes or monitoring
testing . The level of waiting insurance is different , The time of saving logs is also different .
1.3.2 General defect list (CWE)common Weaknesses Enumeration
for example :
CWE-79:XSS Loophole
http://cwe.mitre.org/data/definitions/79.html
CWE-89:SQLi
http://cwe.mitre.org/data/definitions/89.html
A specific type of vulnerability
1.3.3 General vulnerability and disclosure (CVE)Common Vulnerabilities & Exposures
A specific vulnerability http://cve.mitre.org/
for example :cve-2019-0708
1.3.4 Other organizational security vulnerabilities
MS17-010( Microsoft Security Bulletin )
An announcement corresponds to a vulnerability
KB start ( Patches )
S2-053(strtus Safety notice )
strtus2
APACHE Open source development java Framework
1.3.5 Other methodologies
Open source security testing methodology (OSSTMM)
http://www.isecom.org/research/osstmm.html
Information system security assessment framework (ISSAF)
Web Application security joint threat classification (WASC-TC)
Two 、 Penetration testing process
2.1 Penetration test execution standard
Penetration test execution standard (PTES) The pioneers are the elites in the penetration testing industry , There are seven stages , It can be done anywhere
Successful penetration testing in the environment .
http://www.pentest-standard.org/index.php/Main_Page
7 Stages
1、 Prior interaction
2、 Intelligence gathering
3、 Threat modeling
4、 Vulnerability analysis
5、 Exploit
6、 Deep use
7、 written report
Main features and advantages
PTES The main features and advantages of are as follows
1、 It is a very comprehensive penetration testing framework, covering the technical aspects and other important aspects of rope penetration testing , If the scope is too wide
delay 、 The report 、 And how infiltrators protect themselves
2、 He introduced the specific methods of most test tasks , It can guide you to accurately test the security state of the target system
3、 He brings together the rich experience of many penetration testing experts
4、 It contains the most commonly used and rare related technologies
5、 He is easy to understand , You can adjust the corresponding test steps according to the needs of the test work
2.2 General penetration testing framework
From the perspective of Technology Management , Following a formal testing framework is extremely important for security testing , The generic penetration testing framework covers the classic
The various stages involved in the audit test work and penetration test work .
Relevant stage :
Scoping 、 Information gathering 、 target recognition 、 Service enumeration 、 Vulnerability mapping 、 social engineering 、 Exploit 、 Elevated privileges 、
Access maintenance 、 Document report
Whether it's a white box test or a black box test , The selection and use of test steps is the responsibility of the penetration tester .
Before the test begins , The tester needs to test according to the actual environment of the target system and the situation of the relevant target system , finger
Determine the best test strategy .
Scoping
1、 What is the test object ?
2、 What test method should be used ?
3、 What are the conditions to be met in the penetration test ?
4、 What factors may limit the process of test execution ?
5、 How long will it take to complete the test ?
6、 What mission objectives should this test achieve ?
Information gathering
Penetration testers need to use various public resources to obtain relevant information of test objectives as much as possible .
The main channels for collecting information from the Internet are :
Forum | Bulletin board | Newsgroups | The media file | Blog | Social networks | Other commercial or non-commercial websites
In addition, relevant data can be obtained through various search engines .
Such as Google 、 Yahoo 、MSN Bing Ying 、 Baidu, etc
The information collected mainly includes DNS、 The server 、 Routing relationship 、whois、 database 、 E-mail address 、 Phone number 、
Personal information and user accounts .
The more information you collect , The higher the probability of successful penetration test .
target recognition
Identify the status of the target network , Operating system and network architecture 、 Network topology
Service enumeration ( Port scanning )
This stage is based on the results of the previous stages , Further find out all open ports of the target system .
Once all open ports are found , You can list the services running on the target system through these ports .
The open ports on the host have corresponding service programs , After in-depth analysis of this information , The target can be further explored
Possible vulnerabilities in the network infrastructure .
Vulnerability mapping ( Vulnerability scanning )
According to the discovered open ports and service programs , Find known and unknown vulnerabilities
social engineering
If the target network has no direct access , The art of deception will play an important role in attracting jade .
Targeted attacks on personnel of the target organization , It is likely to help us find the entrance to the target system .
for example , A malicious program that entices users to install a backdoor , It may form a breakthrough in the penetration of auditors .
The penetration of social engineering can be divided into many different forms .
Pretend to be a network administrator , Ask users to improve their account information by phone ; Send phishing emails to hijack users' silver
Bank account ; Even induce someone to appear somewhere , These are social engineering attacks
It should be noted that before deceiving the target to achieve the penetration target , In most cases, it takes a long time to study the target person
The psychological
in addition , We need to study whether local laws allow
Exploit
After discovering the vulnerability , You can use the existing vulnerability exploitation program to penetrate the target system
The main task of this stage is to control the target system
This process can be divided into three steps , Before the attack 、 attack 、 Related actions after the attack
Elevated privileges
The penetration tester is based on their access rights , Play at will in the target system ,
Raise the right , Is to upgrade the ordinary user's permission to the administrator's permission
Access maintenance
Most of the time , Auditors need to maintain their access to the target system for a period of time .
That is to bury the back door ( Clear the back door when you leave )
Document report
Auditors should record 、 Report and demonstrate on site what has been identified 、 Verified and exploited security vulnerabilities .
And fix all existing security vulnerabilities according to these documents
2.3 Simplified penetration testing process
1、 Clear objectives
Determine scope | Set the rules | Determining demand
2、 information gathering
Basic information | system information | Application information | Personnel information | Protection information
3、 Leak detection
System FLAW |Web Service vulnerabilities |Web Application vulnerability | Other ports | Communication security
4、 Vulnerability verification
Manual verification | Tool validation | Experimental verification
5、 Exploit
customized EXP| Defense bypasses | To penetrate further | Clean up traces
6、 Form a report
Collation results | Supplementary introduction | Repair suggestions
The general process of hacker attack
0. to grant authorization
1. information gathering
nslookup whois
2. Scan for leaks
namp=ip Range port 80(IIS,apache, What website )scanport
Advanced scanning : Such as IIS Loophole 2003-IIS6.0 2008IIS7.0
Scanning for website vulnerabilities ()
3. Exploit
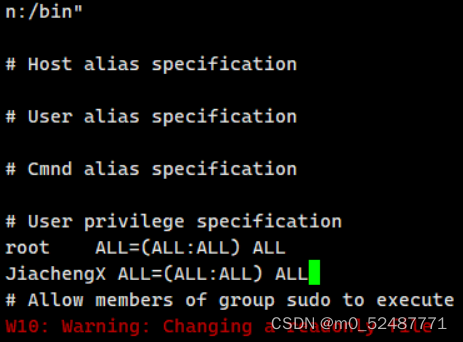
4. Raise the right (shell Environmental Science 、 Desktop Environment 、 Highest authority )
5. Destroy the bodies
6. leave oneself a way out
7. Penetration test report
边栏推荐
- jvm: 方法重载时,具体调用哪个方法,是由传入参数的静态类型来决定的,而不是由参数的实际类型来决定
- The performance of nonstandard sprintf code in different platforms
- PAT 乙等 1025 反转链表
- True MySQL interview question (24) -- row column exchange
- Kotlin android简单Activity跳转、handler和thread简单配合使用
- Low cost 5W wireless charger scheme fs68001b simple charging chip
- How can digital collections empower economic entities?
- Real MySQL interview question (XXVIII) -- case - Analysis of indicators of communication operators
- Software design and Development Notes 2: serial port debugging tool based on QT design
- The author believes that the so-called industrial Internet is a process of deep integration of industry and the Internet
猜你喜欢

Behind the hot digital collections, a strong technical team is needed to support the northern technical team
Raspberry pie assert preliminary exercise

Wechat applet: unfashionable love talk

Lottery DDD code

Opportunities and challenges of digital collections from the perspective of technology development team

Real MySQL interview question (XXVIII) -- case - Analysis of indicators of communication operators

What is the reason for the black screen of the computer monitor when the computer is turned on? What should I do about the black screen of the computer monitor
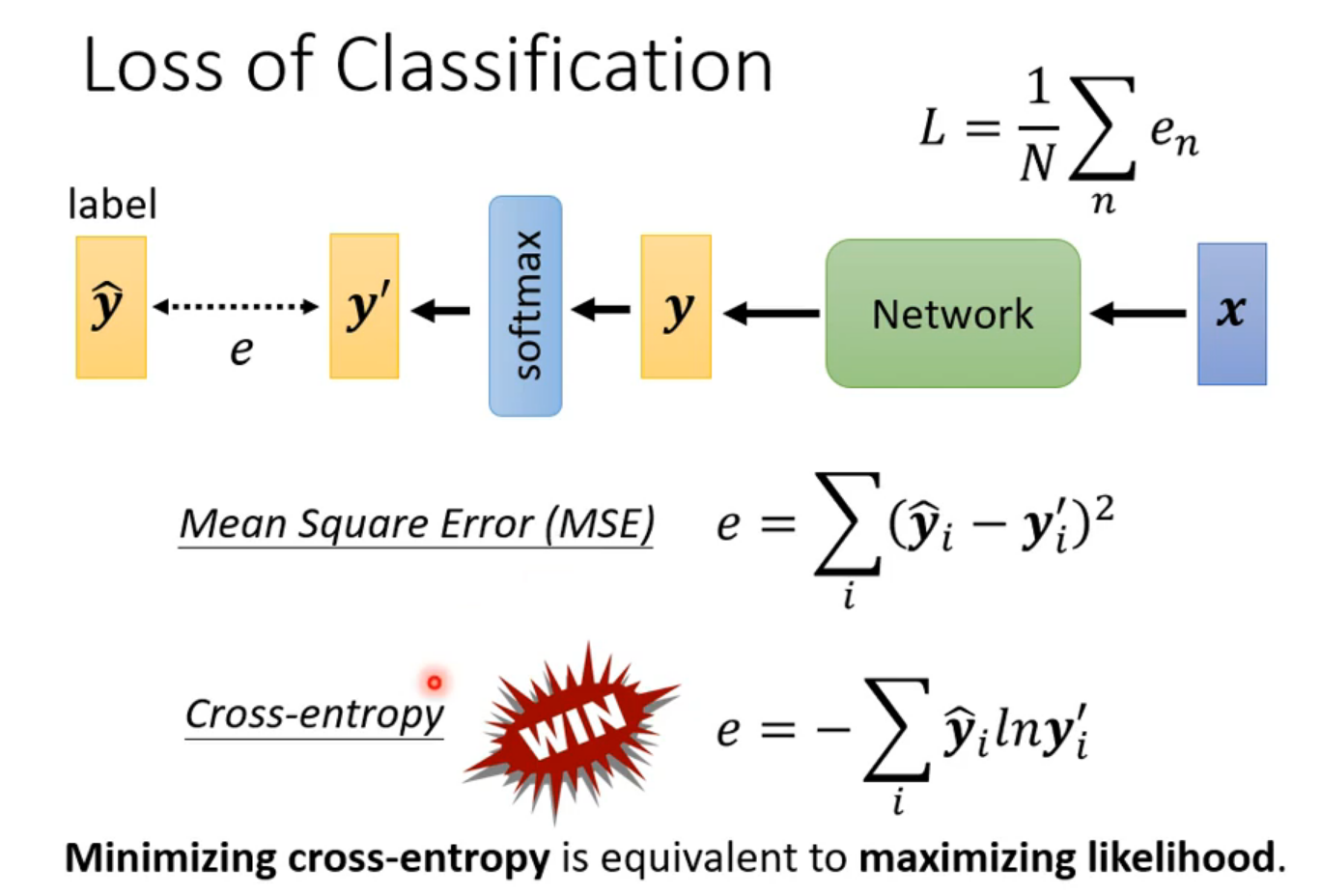
Lihongyi, machine learning 5 Tips for neural network design
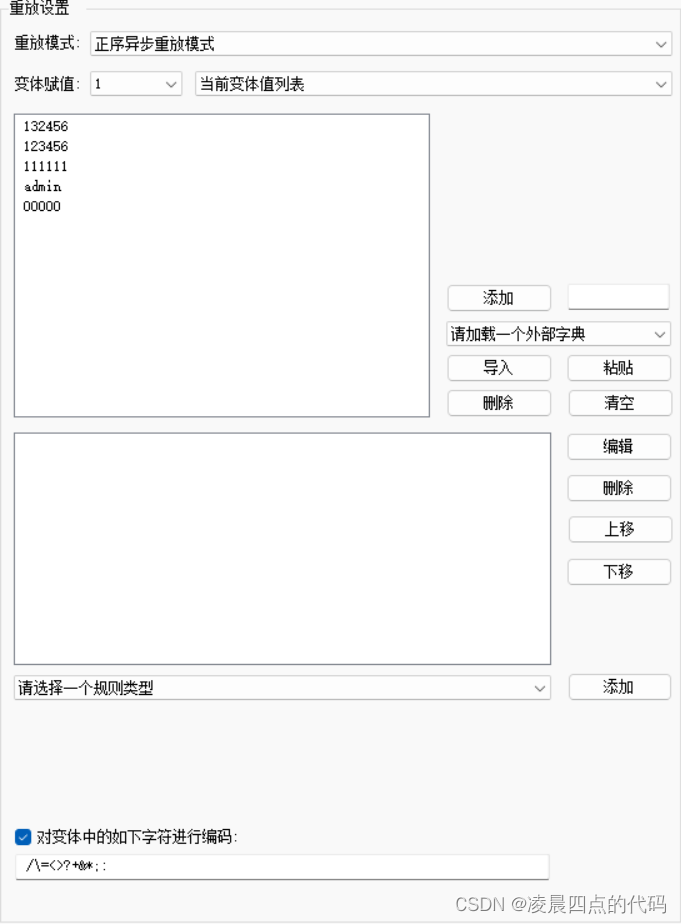
Pkav simple blasting

数字藏品——新的投资机遇
随机推荐
fastjson中的@JSONField注解
Jvm: when a method is overloaded, the specific method to call is determined by the static type of the incoming parameter rather than the actual type of the parameter
Oracle异常
PAT 乙等 1015 C语言
[Stanford Jiwang cs144 project] lab2: tcpreceiver
Raspberry pie assert preliminary exercise
Jsonfield annotation in fastjson
Real MySQL interview questions (XXVI) -- didi 2020 written examination questions
Real MySQL interview question (XXVIII) -- case - Analysis of indicators of communication operators
高等数学(第七版)同济大学 习题1-8 个人解答
Heimdall Database Proxy横向扩展提高20倍
What does the English letter PC mean? What does the Internet PC mean
What benefits have digital collections enabled the real industry to release?
How does win11 enable mobile hotspot? How to enable mobile hotspot in win11
FS2119A同步升压IC输出3.3V和FS2119B同步升压IC输出5V
MySQL面试真题(二十七)——RFM分析法对用户进行分类
Ip6809 three coil 15W wireless charging transmitter scheme IC British chip
Genetic engineering of AI art? Use # artbreeder to change any shape of the image
Wechat applet; AI intelligent dubbing assistant
1010 Radix